Zoom wants to be the new Teams
You think Zoom, you think video calls. For millions around the world, it’s a tool they rely on at work every day.
But for productivity, collaboration and workplace integration (as well as video calls), it’s Microsoft Teams that’s leading the way. Its tight integration with other Microsoft 365 services makes it so easy.
Now Zoom is looking for a piece of that action with the launch of a whole suite of features and services. They’re clearly designed to take on Teams and Slack head-to-head.
These will include email, a calendar app, and a virtual co-working space called Zoom Spots. Meanwhile a bunch of upgrades to the Zoom One platform are aiming to improve collaboration, keep chats flowing, and keep projects moving.
While it feels like a logical step for the video conferencing giant, it remains to be seen how widely adopted the new services will be. And before we recommend it to our clients, we’ll want to know that the levels of support, reliability and security are all bulletproof.
Many businesses are already committed to Microsoft Teams, which releases its own improvements almost on a weekly basis. But this is an interesting new development and we’ll be watching what happens carefully.
If you want to know more about the best tools to keep your team working smoothly together, just get in touch.
Published with permission from Your Tech Updates.






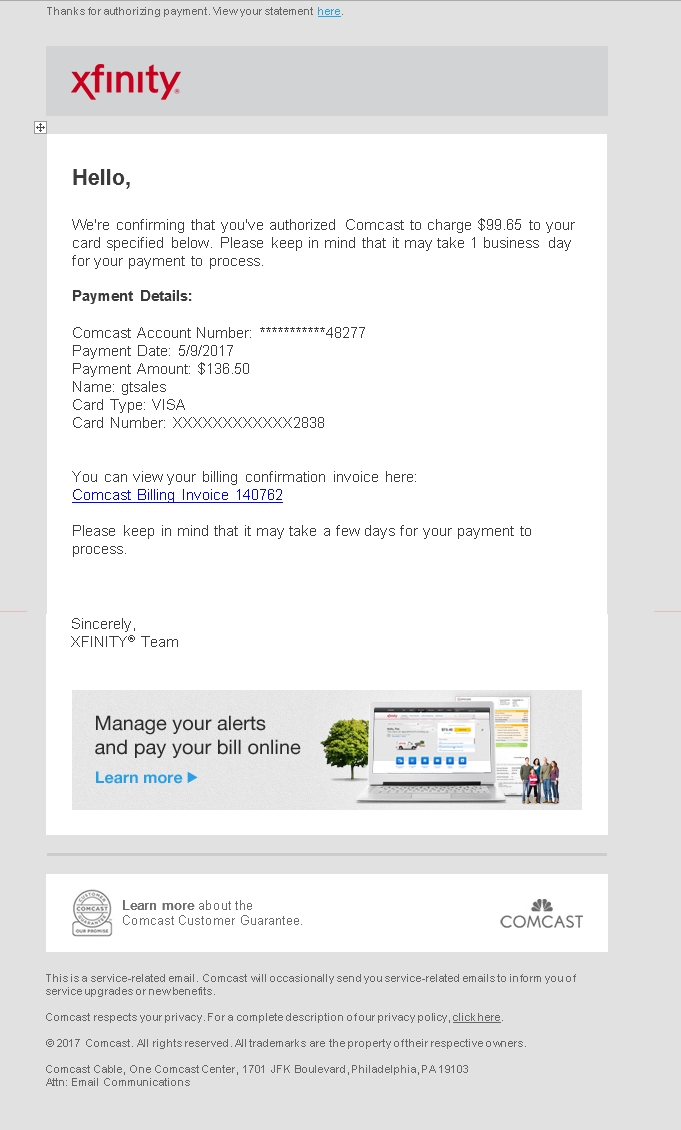
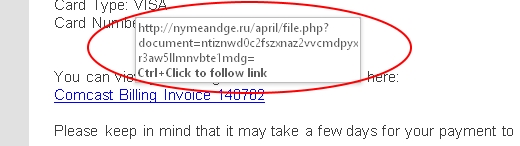
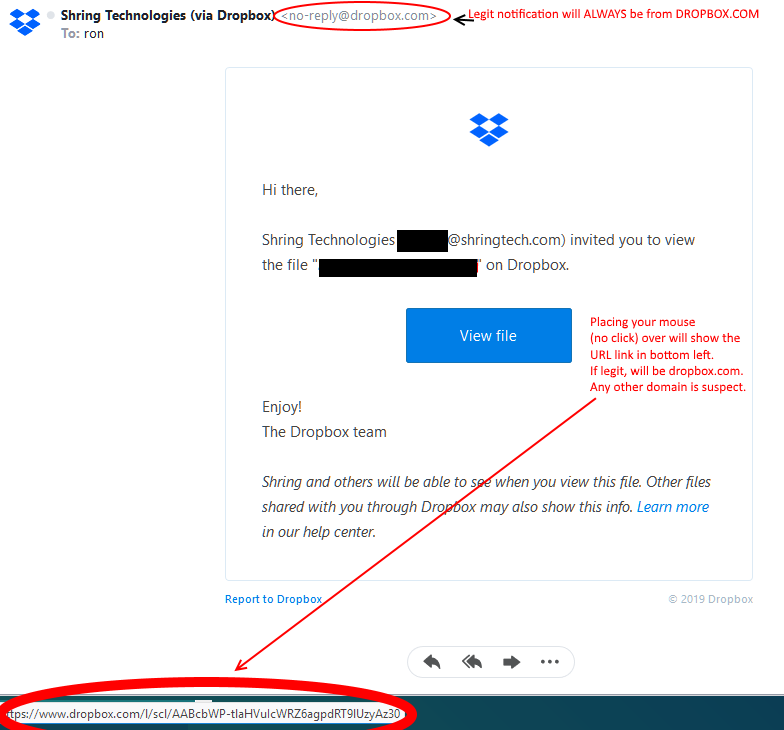 Fake Malicious Dropbox Email:
Fake Malicious Dropbox Email: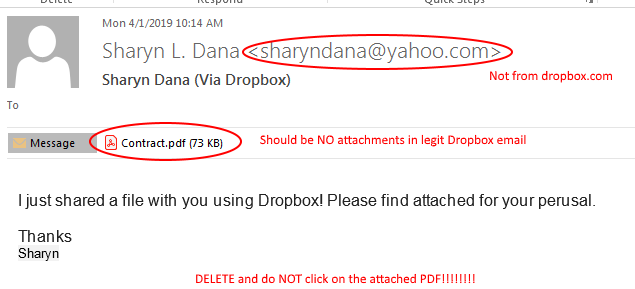 After seeing a legit Dropbox email .. the above screams malicious. However, we get busy and often don’t take the time to actually look at the details. It is now imperative that you scrutinize ANY and ALL emails with attachments. No technology will prevent human overt-rides. I.E. you click on the link and open the PDF .. it is too late!
After seeing a legit Dropbox email .. the above screams malicious. However, we get busy and often don’t take the time to actually look at the details. It is now imperative that you scrutinize ANY and ALL emails with attachments. No technology will prevent human overt-rides. I.E. you click on the link and open the PDF .. it is too late!